The Hybrid Work Era: When Office Boundaries No Longer Exist
We are living in a time when the concept of an “office” is no longer confined within four walls. It can be your living room, a quiet café, or even a seat on a train traveling between cities. Hybrid work has quickly become the new standard, offering greater flexibility and improved productivity for businesses.
However, for IT professionals, this flexibility also introduces a completely new set of security challenges.
In the past, enterprise security was often compared to a “fortress.” Organizations focused on building strong perimeter defenses using firewalls, VPNs, and internal network protections. Once inside the network, users were generally trusted by default.
But in a hybrid work environment, this model no longer works. Company data is now spread across multiple personal devices and accessed through unsecured networks. The concept of a “network boundary” is fading—and with it, new vulnerabilities begin to emerge.
What Is the Zero Trust Security Model?
Zero Trust is a modern security approach built on a simple but powerful principle:
“Never Trust, Always Verify.”
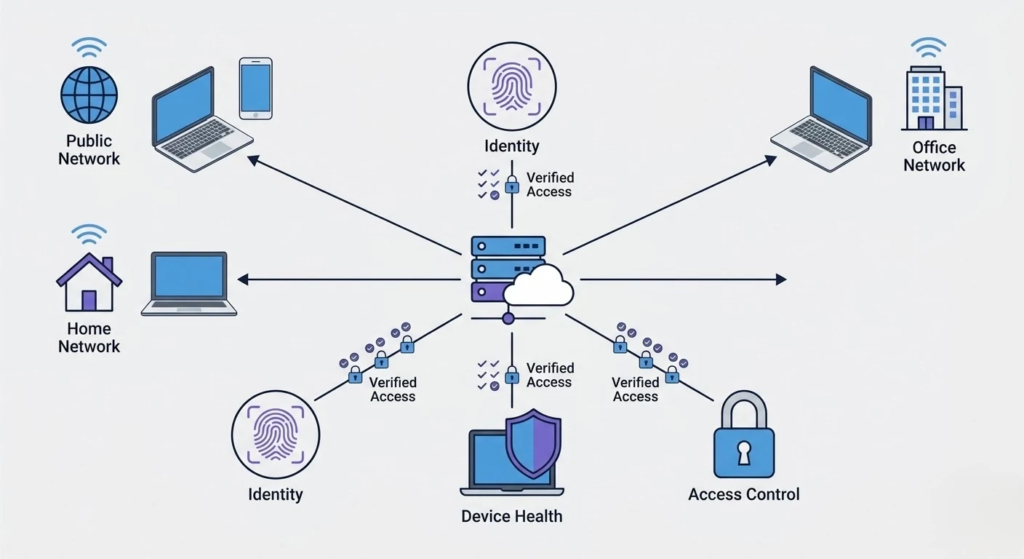
Unlike traditional models, Zero Trust does not distinguish between “inside” and “outside” the network. Every access request is treated as potentially risky and must go through strict verification before being granted.
You can think of Zero Trust like airport security: no matter who you are, you must verify your identity, pass multiple checkpoints, and follow strict procedures before boarding a plane.
The Three Core Pillars of Zero Trust in Hybrid Work
To effectively implement Zero Trust, organizations need to focus on three key areas:
Identity Verification
In a Zero Trust model, identity becomes the first and most critical layer of defense.
Traditional passwords are no longer sufficient. Organizations must adopt stronger authentication methods such as multi-factor authentication (MFA), biometrics, and contextual authentication based on device, location, and behavior.
This ensures that the person requesting access is truly who they claim to be.
Device Health Control
Zero Trust does not only verify users—it also evaluates the devices they use.
Before granting access, the system checks whether the device is secure:
- Is the operating system up to date?
- Is security software installed?
- Are there any signs of compromise?
If a device does not meet security standards, access is denied immediately.
Least Privilege Access
Another fundamental principle of Zero Trust is limiting access rights.
Users are only granted access to the resources they actually need—nothing more.
For example, developers should not have access to financial data, and HR staff should not access backend systems. This significantly reduces potential damage if an account is compromised.
Traditional VPN vs. Zero Trust
The differences between these two models can be summarized as follows:
- Traditional VPN trusts users once they are inside the network, while Zero Trust assumes no implicit trust.
- VPN controls access based on network location, whereas Zero Trust focuses on identity and device validation.
- VPN systems are harder to scale, while Zero Trust is more flexible and cloud-friendly.
- Security risks are higher with VPN if compromised, while Zero Trust minimizes potential damage.
- User experience in Zero Trust environments is generally smoother and less dependent on centralized connections.
Case Study: How Zero Trust Stops a Ransomware Attack
Imagine the following scenario:
An employee at Company A is working remotely using a personal laptop. During use, the device unknowingly downloads software infected with ransomware.
In a traditional security model:
- The employee connects via VPN and gains full access to internal systems
- The malware spreads and encrypts company data
However, with Zero Trust:
- The system detects that the device does not meet security requirements
- Access is immediately denied
- The attack is stopped before it can cause damage
This illustrates the critical difference between the two approaches.
Getting Started with Zero Trust: Where Should Businesses Begin?
After understanding Zero Trust, the most common question becomes: “Where do we start?”
In reality, Zero Trust is not something that can be implemented all at once. It is a journey that requires organizations to gradually rethink their security approach—from mindset to infrastructure.
This journey can begin with four essential steps:
Understand What Needs Protection
The first step is not buying tools, but identifying what matters most.
Not all data holds equal value. Businesses must determine which assets are critical—customer data, internal systems, APIs, and strategic documents. Once identified, security efforts can be focused where they matter most.
Strengthen Authentication Layers
Passwords alone are no longer enough.
Organizations should implement stronger authentication mechanisms such as MFA, biometrics, and contextual verification. This ensures that access is granted to the right person—not just someone with the correct credentials.
Proactively Manage Device Security
In a hybrid work environment, personal devices become part of the enterprise ecosystem.
Businesses must ensure that all devices meet security standards—regular updates, antivirus protection, and anomaly detection. Device management solutions (MDM) can help automate and maintain this process effectively.
Limit Access to What Is Necessary
Zero Trust emphasizes granting only the access that is truly required.
Instead of broad permissions, organizations should review and refine access rights based on roles. This significantly reduces risks and limits damage in case of a security breach.
In Summary
Zero Trust does not require businesses to change everything overnight. But by starting with the right steps—understanding assets, verifying identities, securing devices, and controlling access – organizations can build a strong foundation for modern security.

Why Zero Trust Is No Longer Optional
Zero Trust is not just a technology trend—it has become a necessity.
It helps organizations protect sensitive data from increasingly sophisticated cyber threats, while enabling employees to work flexibly from anywhere. At the same time, it enhances visibility and control for IT teams and reduces internal risks, which are often the root cause of major security incidents.
Conclusion
The way we work has changed – and so must the way we secure our systems.
In the era of hybrid work, relying on traditional security models is like leaving the door open for attackers. Zero Trust is not just a technical solution, but a foundation for secure, flexible, and sustainable business operations.
At Linnoedge, our IT team continuously researches and adopts modern security standards to ensure the highest level of protection for our clients’ systems and data.
Furthermore, as businesses increasingly adopt artificial intelligence to automate processes and boost productivity in this hybrid era, the attack surface naturally expands. AI models and the vast amounts of sensitive data they process must also be strictly protected under the Zero Trust framework. Ensuring that AI tools are securely integrated and continuously monitored is no longer optional—it is a crucial component of a resilient cybersecurity strategy.
To learn how we can help you safely implement AI into your workflows, explore our AI solutions and security consulting.
Ready to enhance your security strategy? Contact us today to get started.
